Navigating the Bow Shock: Understanding its Impact
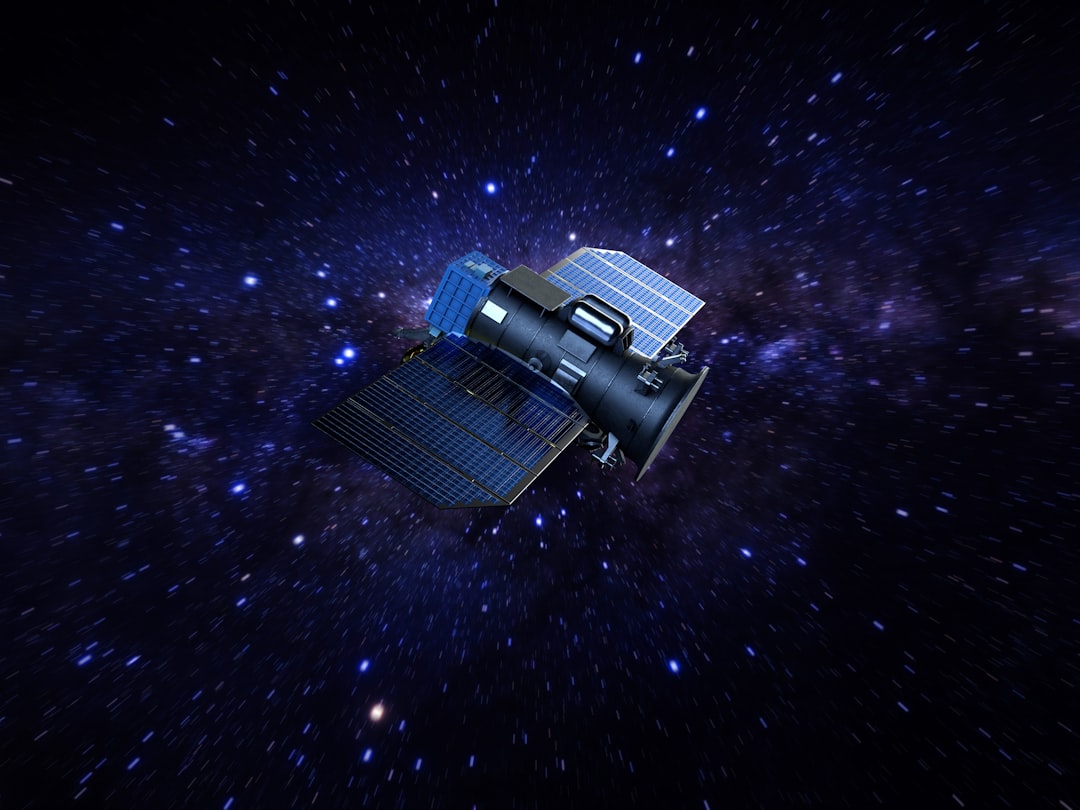
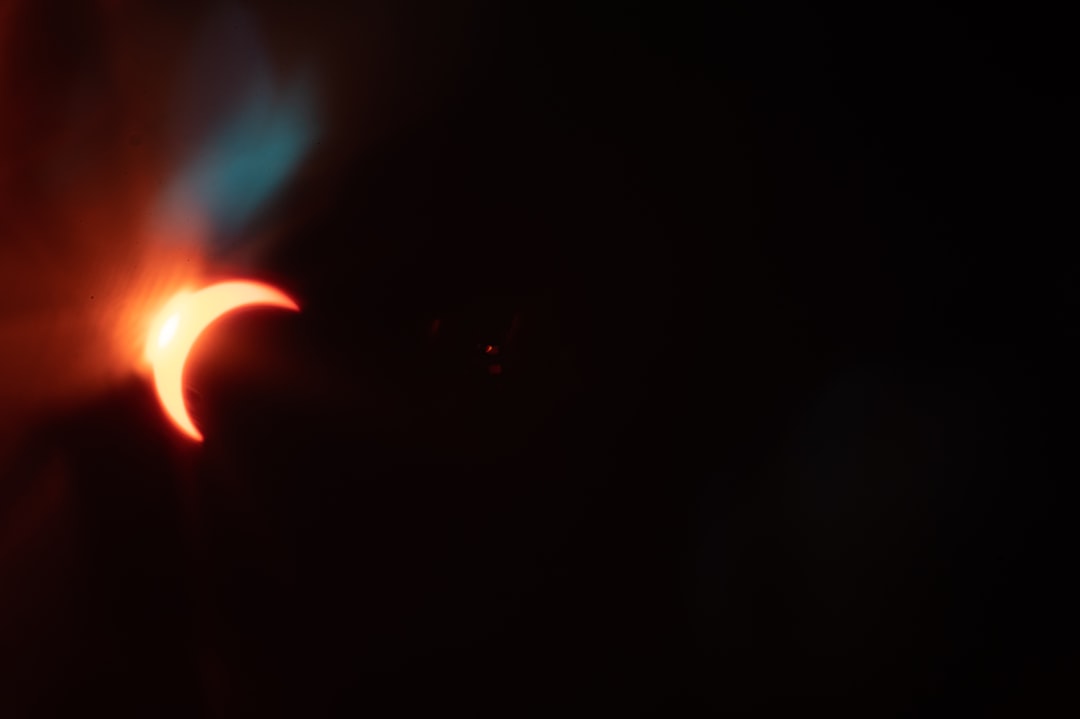
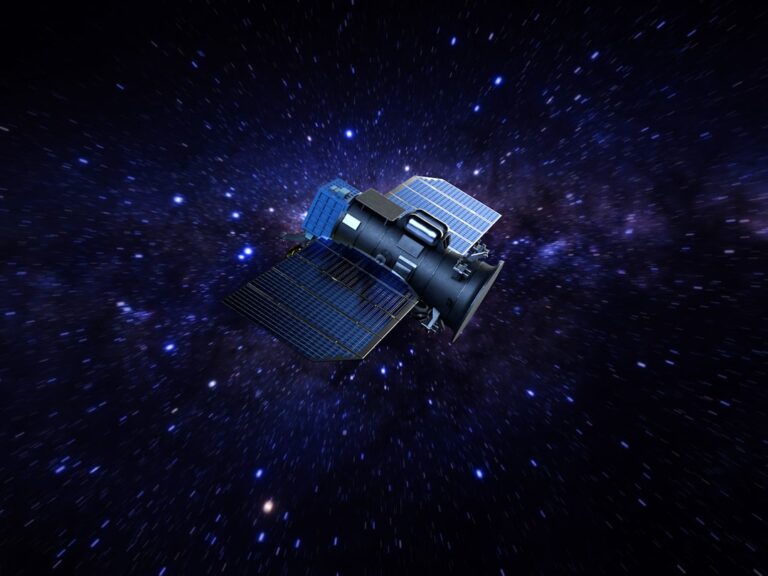
The bow shock is a fascinating phenomenon that occurs in space, particularly when a solar wind—a stream of charged particles emitted by the sun—interacts with a planet's magnetic field. Imagine a boat moving through water; as it cuts through the waves, it creates a bow wave in front of it. [more ...]
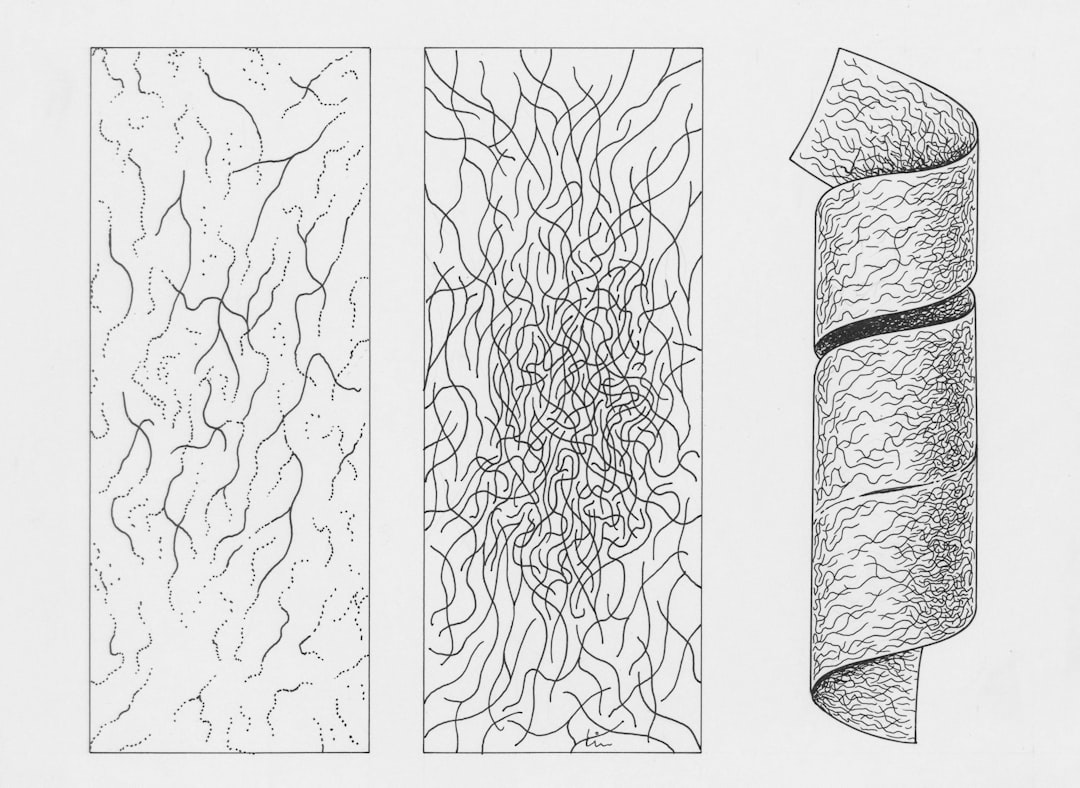
Understanding the Earth’s Magnetosphere
The Earth's magnetosphere is a fascinating and complex region that plays a crucial role in protecting our planet from harmful solar and cosmic radiation. Essentially, it is the area around Earth that is influenced by its magnetic field, extending thousands of kilometers into space. This magnetic shield is not just [more ...]
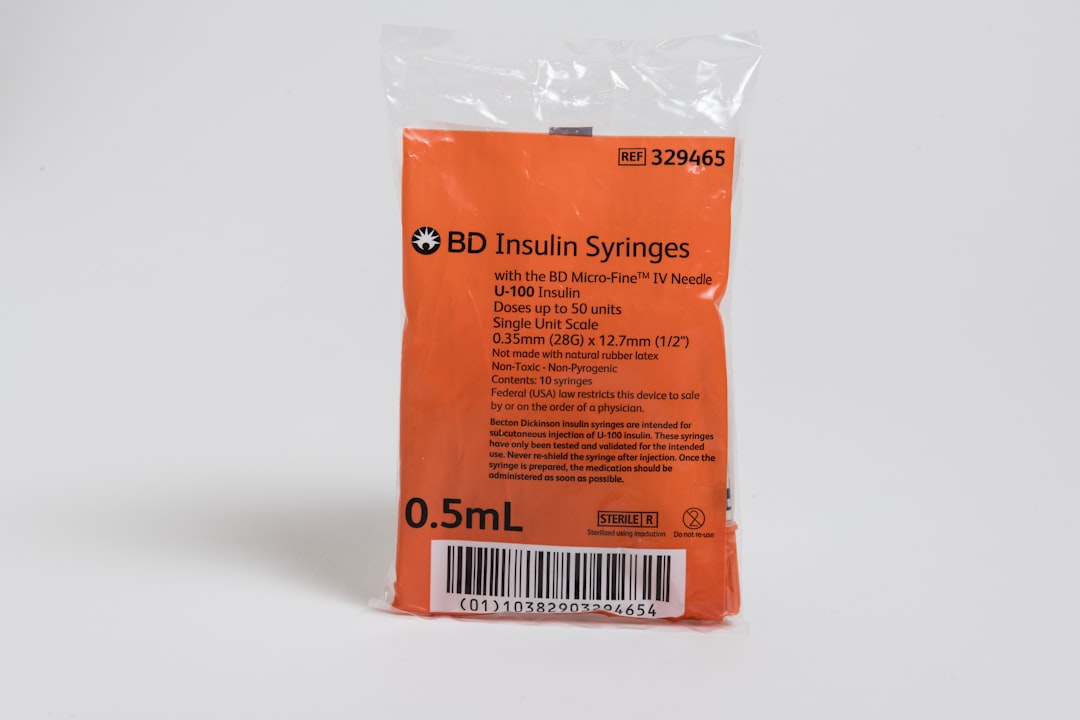
Harnessing the Power of Plasma for Medical Treatment
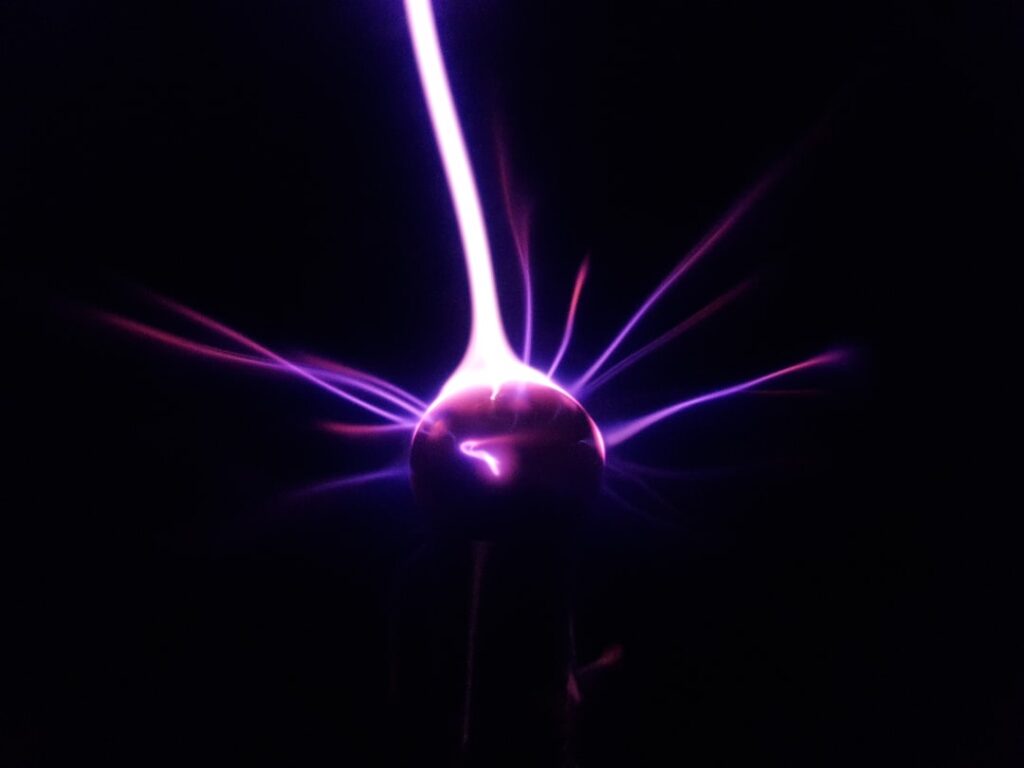
Plasma is often referred to as the fourth state of matter, alongside solid, liquid, and gas. It consists of ionized gas, where a significant portion of the particles are charged ions and free electrons. This unique state of matter is not just a scientific curiosity; it plays a crucial role [more ...]
Discover Warehouse Jobs Near Me
Warehouse jobs play a crucial role in the supply chain, serving as the backbone of logistics and distribution. These positions are essential for managing inventory, fulfilling orders, and ensuring that products reach consumers in a timely manner. The work environment can vary significantly from one warehouse to another, ranging from [more ...]